When faced with rebuilding your outdated custom software solution from scratch or re-creating it via multiple existing SaaS solutions, it's no shock that many business experts choose the latter. SaaS solutions aren’t just “easier” to navigate, they also present a rare opportunity for teams to take control of their “technological destiny” and improve upon processes with new or more modern tools they choose for themselves (rather than being given by an IT team).
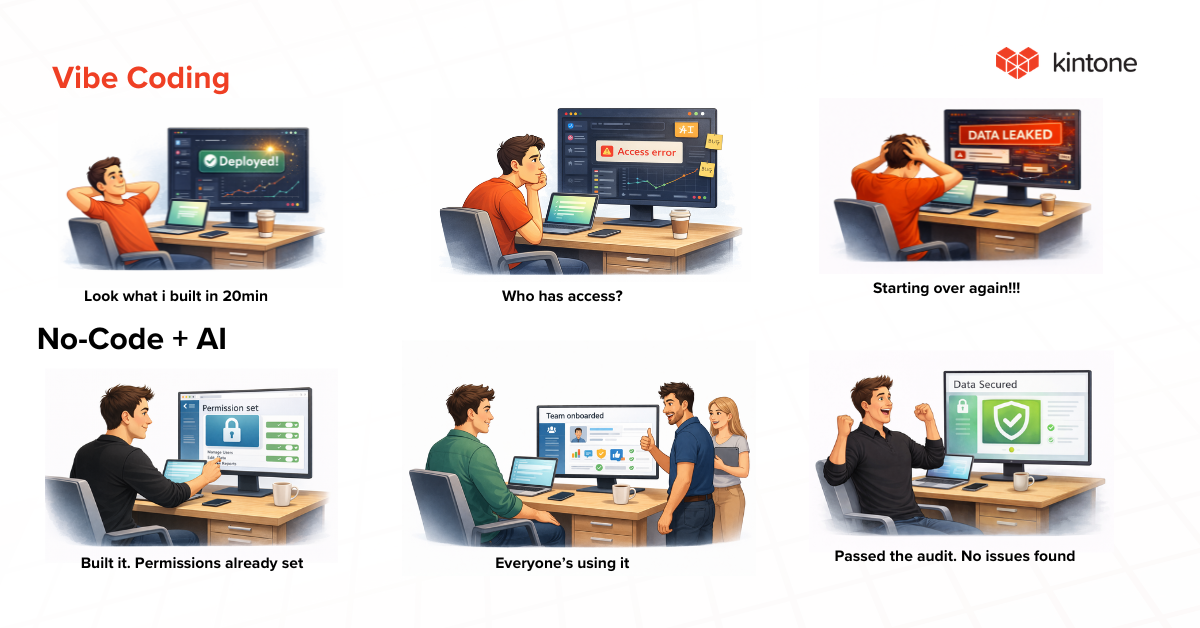
But this newfound freedom doesn’t come without risks. Here’s why the age of SaaS has IT teams sweating:
It creates opportunity for the rise of Shadow IT
What is Shadow IT?
Shadow IT consists of any application, program, or system that a company builds or buys without IT oversight. It can be a monthly subscription to applications, like Slack or Dropbox, or department-specific apps like Salesforce or Zendesk. Apps like these—or ones built in internally—are largely ungoverned, rarely officially approved by the company, and significantly increase technology spend.
Why is Shadow IT bad for business?
The answer has many parts. Let’s look at the top six:
It doesn’t give your IT team the ability to prepare for threats
IT is charged with governance and readiness. They can't protect against risks about which they don't know. This is one of shadow IT's most serious implications. And if you think CIOs are wise to the game, think again.
A CISCO survey asked CIOs to estimate the number of cloud applications and services running across the organization. They answered 51. The actual number was 730. Even in heavily regulated environments like healthcare, the survey found 17 to 20 times more cloud apps running than IT estimates. If IT isn't in control, who is? Are the inmates running the asylum?[1]
More software creates more potential points of failure
More applications mean more risk. Even if you secure the infrastructure, every application provider adds a new line to your list of things that must be monitored, patched, and protected. In a survey of vulnerabilities reported in 2018, a quarter of them were business applications. And the rise of open-source software and libraries has given bad actors even more entry-points into an organization.[2]
Your business’ workflows depend on too many uncontrolled factors
The operational risk is combined with the need to rely on the stability of every vendor. This gets harder to do with a market crowded with lots of mid-range entries.
Using tools built to open standards is one hedge: you can at least re-purpose information and assets. But it's hard to make long-term strategic business and technology plans around a tool you don't have full confidence has a long shelf span.
Your team spends less time innovating, more time managing data sharing
More applications mean more places data lives as an input and output. And scattering information between tools makes it harder to start to leverage that information in meaningful ways like AI/ML. Read about data de-duplication to understand the fundamentals of that challenge.
Organizations that are 'earlier' in their transformation journey should view integration as a meaningful half-step. Investing in a single point solution rarely is.
It kills collaboration between teams by spreading conversation across platforms
Being able to move quickly from a task to communications is the sign of a seasoned team. Spreading tasks across multiple tools make this harder, spreading conversations across multiple tools makes it worse. When one part of a team or department is on Slack, another is on Google Hangouts, and another relies on Skype or Zoom, you have a fundamental problem at hand: the conversations are happening, but there’s no place where that collaboration can be seen or shared by/with anyone else. Standardized collaboration tools are a bare minimum requirement for any digital success at scale.
This is doubly critical for distributed organizations where team members don't share physical space.
Inability to get the big picture on what all your data is saying
Technology's ability to optimize your business is undercut when it's hard to find objective standards of measurement. If one third of your data lives on one solution, while fractions live on several others, getting it all into one report for a comprehensive view is either impossible or requires hours of menial patchwork effort by members of your team (hello, Excel version bingo from Hell).
You are creating meaningful metrics that help you learn what you're doing right and where you can improve. Those sorts of big picture lessons can get lost in too many details.
Shadow IT is a symptom of a greater problem
Shadow IT comes with its range of problems. Why, then, do so many companies still struggle with it? And why are individuals so quick to take on the risks (even knowing them) to use new tools?
The answer is results. Many Shadow IT solutions, for all their risks and problems, fill the gaps many traditional software solutions can’t or don’t. A bank that uses a software solution made in 2001 may no longer have all the features its employees need to complete their 2020 tasks. So what do they do? Find workarounds. After all, it’s faster and easier to buy a few licenses for a couple hundred dollars rather than ask an overloaded IT team to modify a custom solution with years of data and tens of thousands of pieces baked into it.
So what does Shadow IT really point to? Two things:
The demand for technology that responds to market changes & demands
The way we do business is constantly changing, and technology is often at the core of those developments. What we did on paper fifteen years ago we now do online but across four or five different platforms. And even those platforms are changing as vendors close and new ones open, or as technology shifts. Look at the rise and fall of Flash, for example.
But when our technology can’t change with us, it becomes a weight around our ankles. Unfortunately, no employee can point to their tools as the reason for not being able to do their tasks. So they find workarounds using new tools that can help them keep pace with demand.
This need for tools that can adapt to the circumstances is dire. If companies can’t find a way to keep their resources responsive, then Shadow IT is given.
The need for software that can be highly customized to any specific workflow
Old technology or technology made to appeal to as many departments/tasks/groups as possible often comes with very rigid limits in how custom it is. It offers a wide array of features, but these features are often generic; they don’t serve the very specific workflows a team or particular user needs, at least not without requiring the user to jump through several extra, unnecessary steps.
Shadow IT tools are a sign that teams have very specific workflows their current resources cannot accommodate. It means the team is currently creating extra steps (say data transfer between two platforms using an Excel sheet) in order to reduce some of the roadblocks or other steps their original system created.
What all this points to is the need for customization: tools that can be task-specific and are flexible enough to do exactly what individuals need, not just entire departments or the company as a whole.
How can one get flexibility and customization without chasing Shadow IT solutions?
By considering tools that prioritize striking a balance between security & agility
Significant advances in how software gets built are changing what gets built. New tools and development platforms are giving companies the ability to work inside one singular ecosystem that supports all their needs: security, flexibility, management, and maintenance. Better yet, these platforms can deliver these functions and features via highly customizable workflows and interfaces.
What would this kind of ecosystem look like?
Let’s pretend there’s a marketing team for a SaaS product that needs to produce more customer stories. Marketing team member Joanne realizes she needs the support of customer support and sales in order to identify the customers who are ready to give their story. The data she needs to write her story includes the customer’s name, the features they use, the particular pain points they faced, and how many people use the product.
Right now, there’s no process built for this. But this doesn’t stop Joanne; she sits down and outlines what the steps would be, what information she needs at each step, and who will be responsible/involved along the way.
Here’s what a basic flowchart might look like.
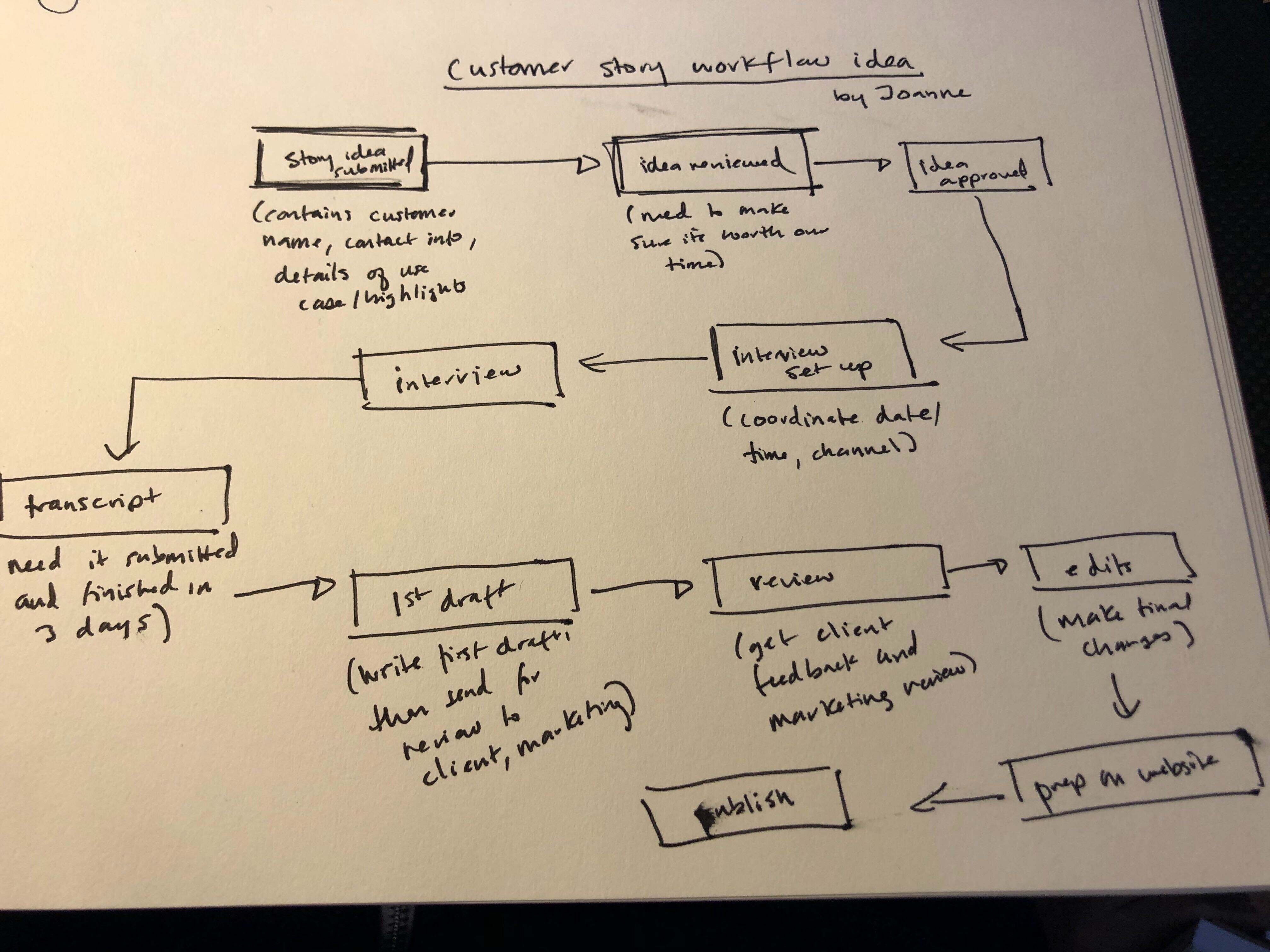
Once she has her requirements clear, she opens up the current company-approved software she works in and hits CREATE. Then, without code or an IT team over her shoulder, she builds this brand new workflow herself in the matter of an hour or two. When it’s done, she launches it. Now it’s ready for use. Joanne begins acting out the new workflow once she’s told the other teams what to expect.
Because her new workflow is built within a company-approved ecosystem, it doesn’t fall outside the oversight of IT (and thus become Shadow IT). Her new workflow also doesn’t require new software adoption, since it’s created in a pre-existing enterprise software platform. Best of all, it’s something she can build without needing to check in with developers, IT, or any other kind of software expert before doing so. She knows what she needs: rather than trying to communicate that to someone else and waiting for them to build it, she can get busy designing exactly what she wants herself, no extra persons required.
Joanne is using is a tool that:
- Allows her to create new workflows in response to new needs
- Build it herself without relying on IT or third party developers
- Get the customization she wants without wasting time researching new tools
- Create the flow she wants without putting her data or the company’s security at risk
What kind of tool allows this?
No-code/low-code platforms give teams everything they want from their Shadow IT solutions without the risks that come with them. Think of these platforms as ecosystems that support and maintain a fluctuating number of highly-interconnected needs: your IT team’s need for security, your need for flexibility, and your company’s need for results. And they do so without generating the same costs traditional custom software solutions require.
How do no-code/low-code platforms do this?
By giving you a secure digital sandbox in which you can build the type of business software you need. Cloud-based no-code/low-code platforms work like a blank check: they can be created to be whatever the user wants. Even better, users of any technical level can easily learn and use them to build what they need.
The reason these platforms are so widely accessible are their visual programming features. Visual programming tools don’t fill your screen with lines of code text. Instead, the user interface is, as the name suggests, visual.
The act of programming consists of dragging and dropping graphics, just like you do in many of your favorite consumer websites, social media tools, and apps. While WYSIWYG editors and similar tools are a form of visual programming, in this case the technology is being reapplied. You’re no longer using those tools to add cute lines and colors to text—you’re using them to build powerful, customizable databases and workflow optimized to meet your specific needs. And, you can start using them the second you’re done building them.
How do these platforms counter shadow IT concerns?
No-code/low-code platforms like Kintone give users the ability not just create custom workflows and databases for their needs—it’s visual programming interface means they can be built, maintained, and modified in real time as the user needs.
Which means no waiting on development. Changes happen as soon as they’re needed.
Such immediacy, combined with the platform’s sheer flexibility, eliminates the need for individuals to seek out new software from other providers. They can simply make what they want themselves. Even better, what they make doesn’t need to be connected to any of their databases via REST APIs or other tools. It all rests in the same ecosystem as their other workflows, meaning users don’t fragment their data or database to get the workflows they need.
No-code/low-code platforms make Shadow IT inconvenient.
Want to learn more about how no-code/low-code platforms are improving the way we work with software to get our jobs done? Read our ebook, “We’re All Software Developers Now: Why the Next Programmer Joining Your Company is You.”
You’ll learn not just why software development is becoming more accessible, but how you can utilize this change to be more valuable and effective in your role.
About the Author
Michelle is the Content Marketing Specialist at Kintone. She is a content marketing expert with several years in content marketing. She moved to San Francisco in 2015 and has experience working in small businesses, non-profits, and video production firms. She graduated in 2012 with a dual degree in Film and English.